The U.S. National Cybersecurity and Communications Integration Center describes the Insider Threat as a current or former employee, contractor, or any type of business partner, who has or had authorized access to your organization’s networks, systems, and data – who then misuses such access to the detriment of your confidentiality, integrity or availability. Manifesting as theft, sabotage, fraud, or espionage, such actions represent a serious daily risk to your operations and business success.
Integrity ISR uses our collective knowledge of the Insider Threat environment to develop a comprehensive, enterprise-wide analysis.
COMPREHENSIVE THREAT ASSESSMENT
- Determine the existing threat environment; analyze critical assets and supporting infrastructure; and review client, vendor and contractor relationships
- Analyze your ability to detect Insider Threats by examining governance and employee-focused capabilities (hiring practices, monitoring, and awareness)
- Review your capabilities to deter Insider Threats, focusing on programs, procedures, control mechanisms, and training
- Explore your capabilities to effectively respond to an Insider Threat through a gap analysis identifying overall strengths, weaknesses, and vulnerabilities
- Provide Persistent Monitoring services to protect your enterprise, and increase full spectrum threat understanding
We start with an examination of the threat, evaluate existing programs, strategies, training and monitoring procedures to determine the “as is” status. We develop an enterprise-wide gap analysis report, work with the client to optimize a scalable insider threat management plan, and then propose and deploy a risk mitigation plan. Plus, we offer customized, full spectrum Insider Threat Training for every level of your enterprise. These steps are fully scalable and tailorable to meet your requirements, respect host nation laws and customs, and provide discreet recommendations in challenging work environments. Our work is done in a confidential manner with signed Non-Disclosure Agreements to protect all of your proprietary data and materials.
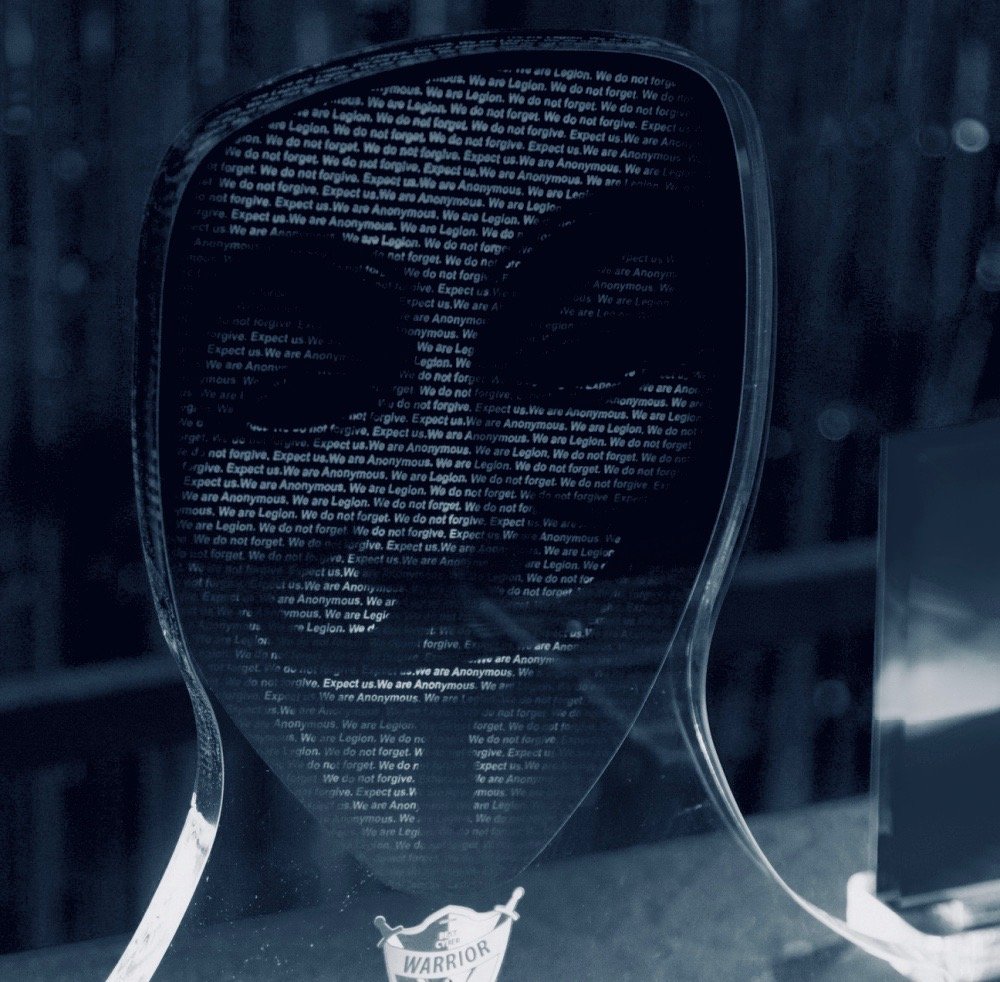
#CombatProven
